Industrial IoT security gaps often start with legacy devices
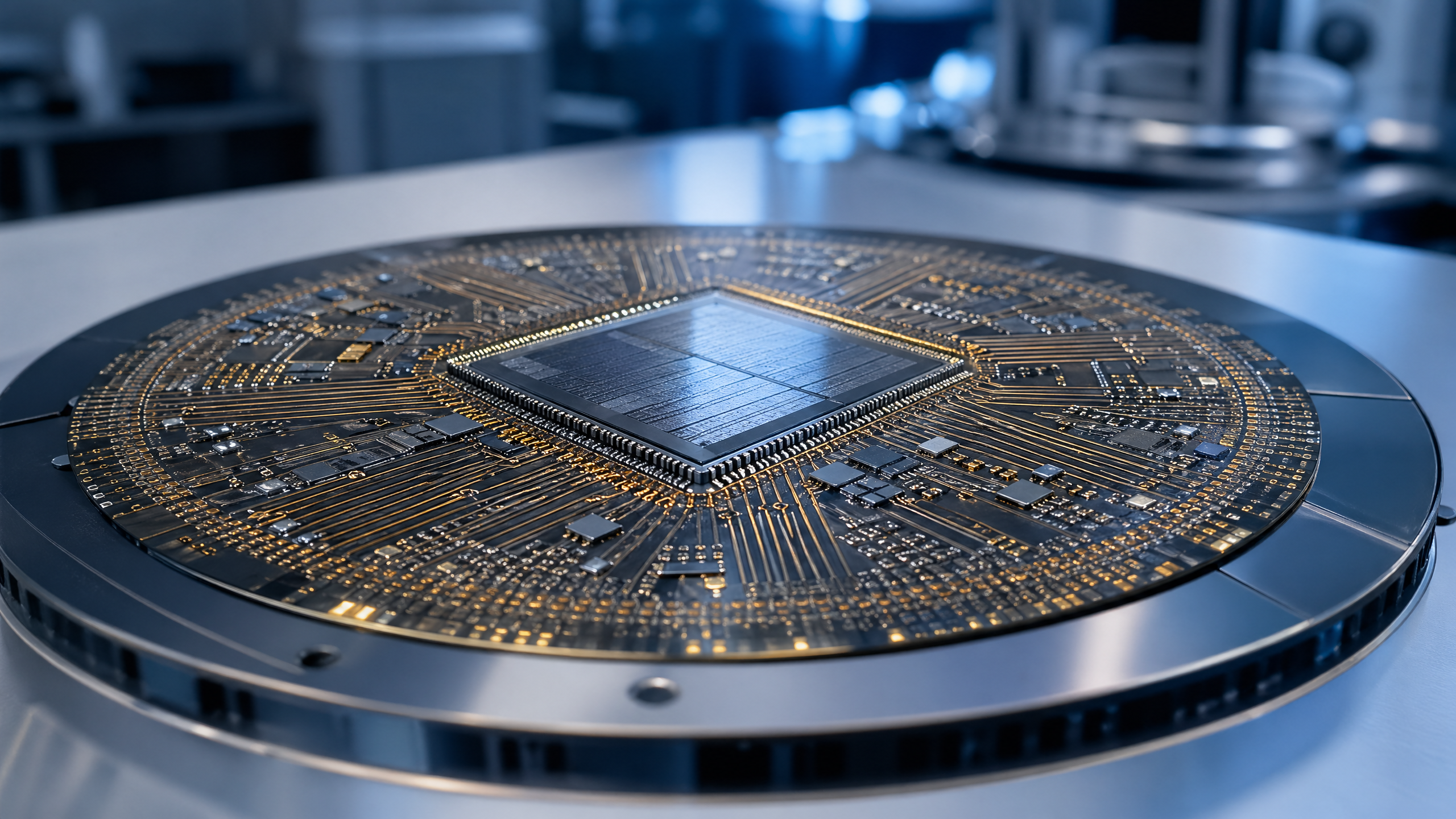
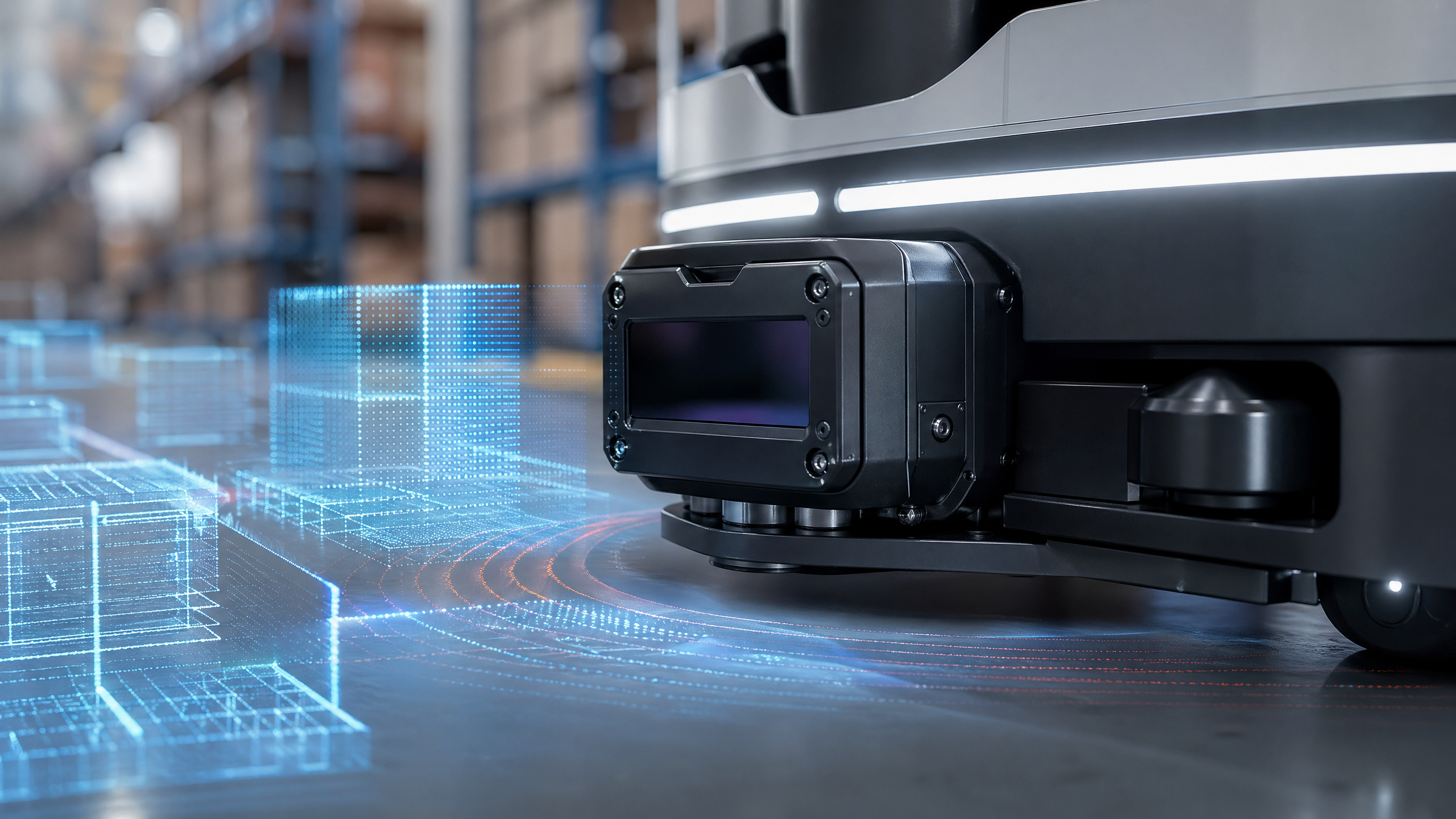
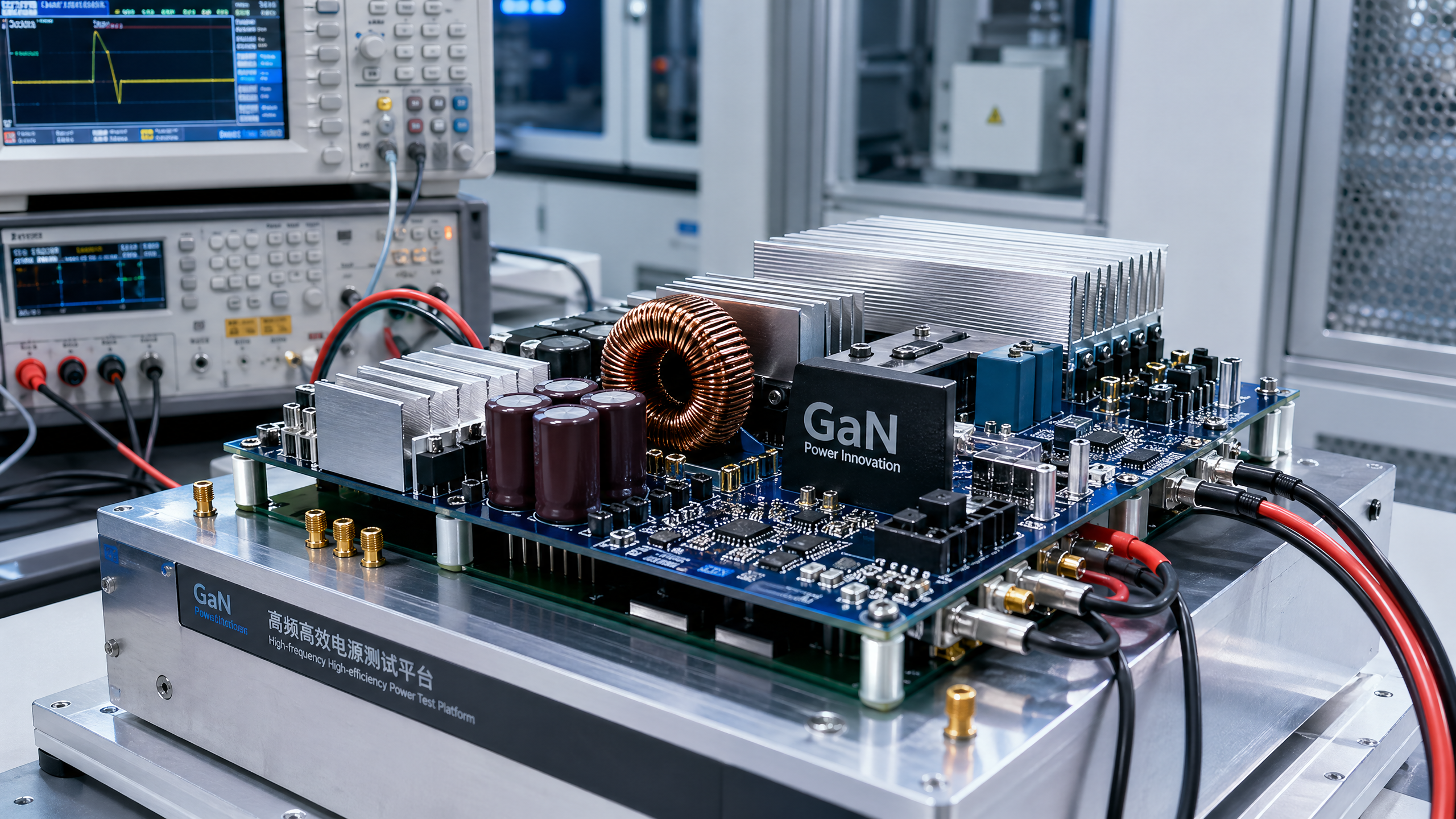
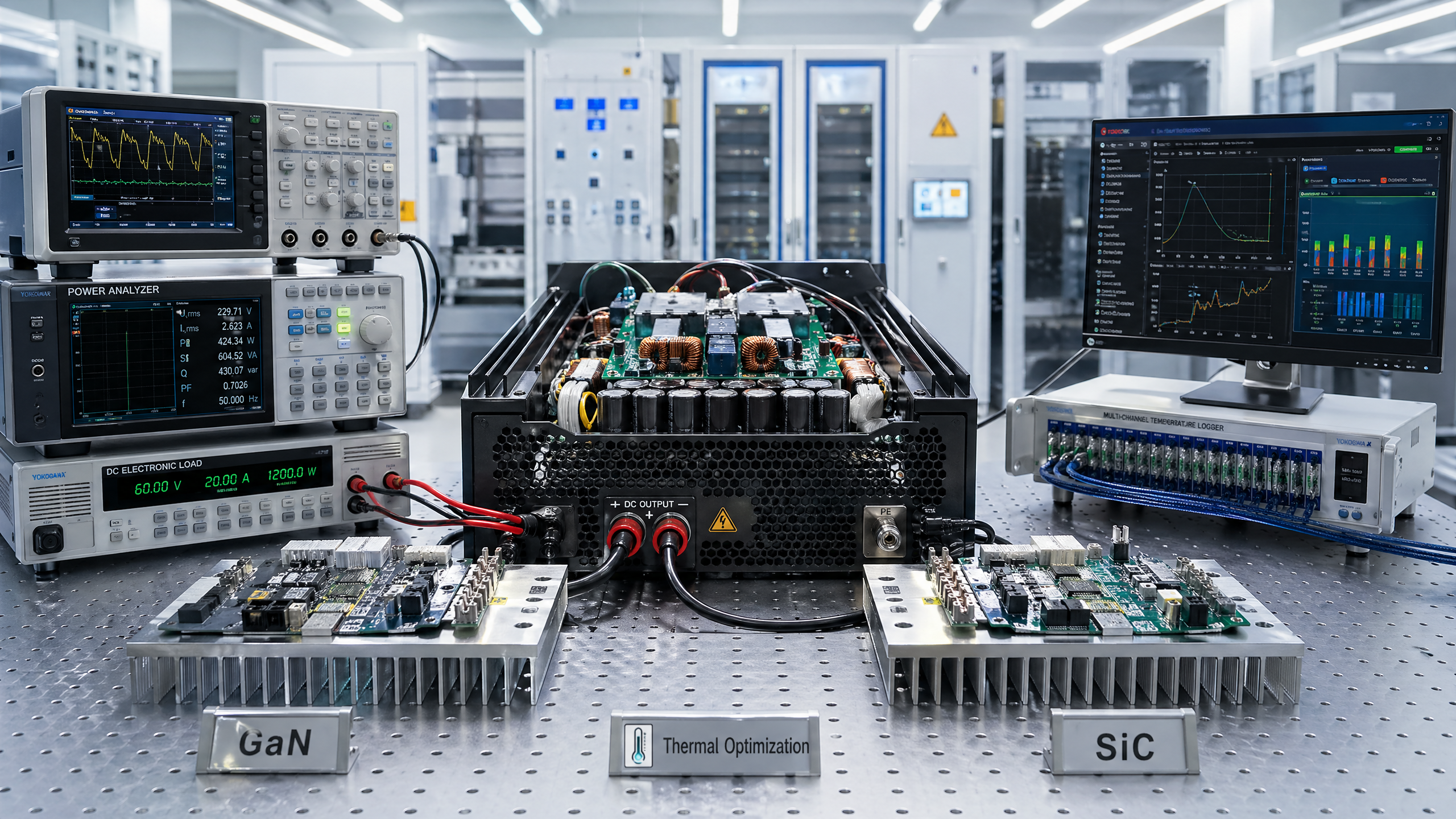
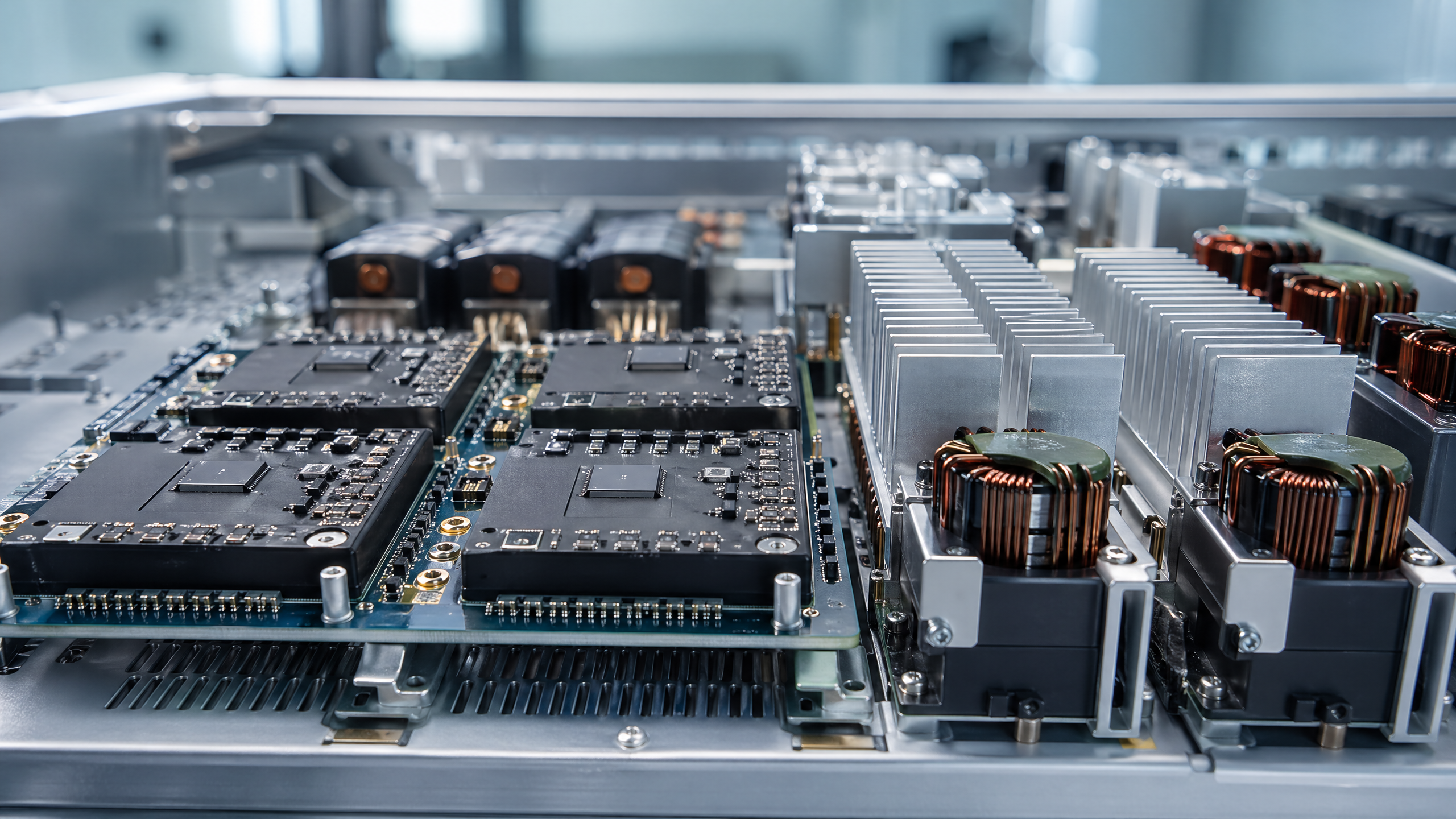
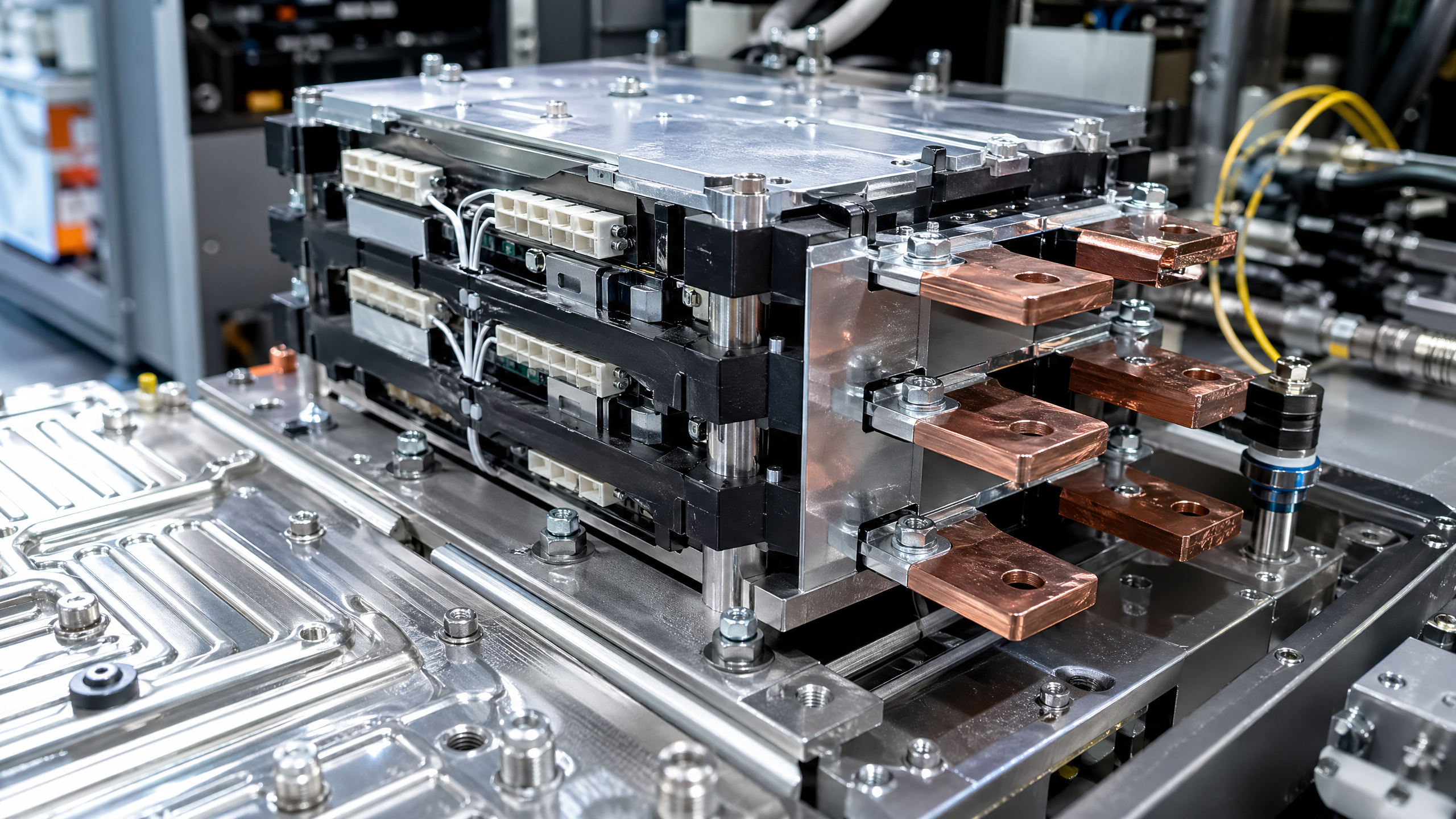
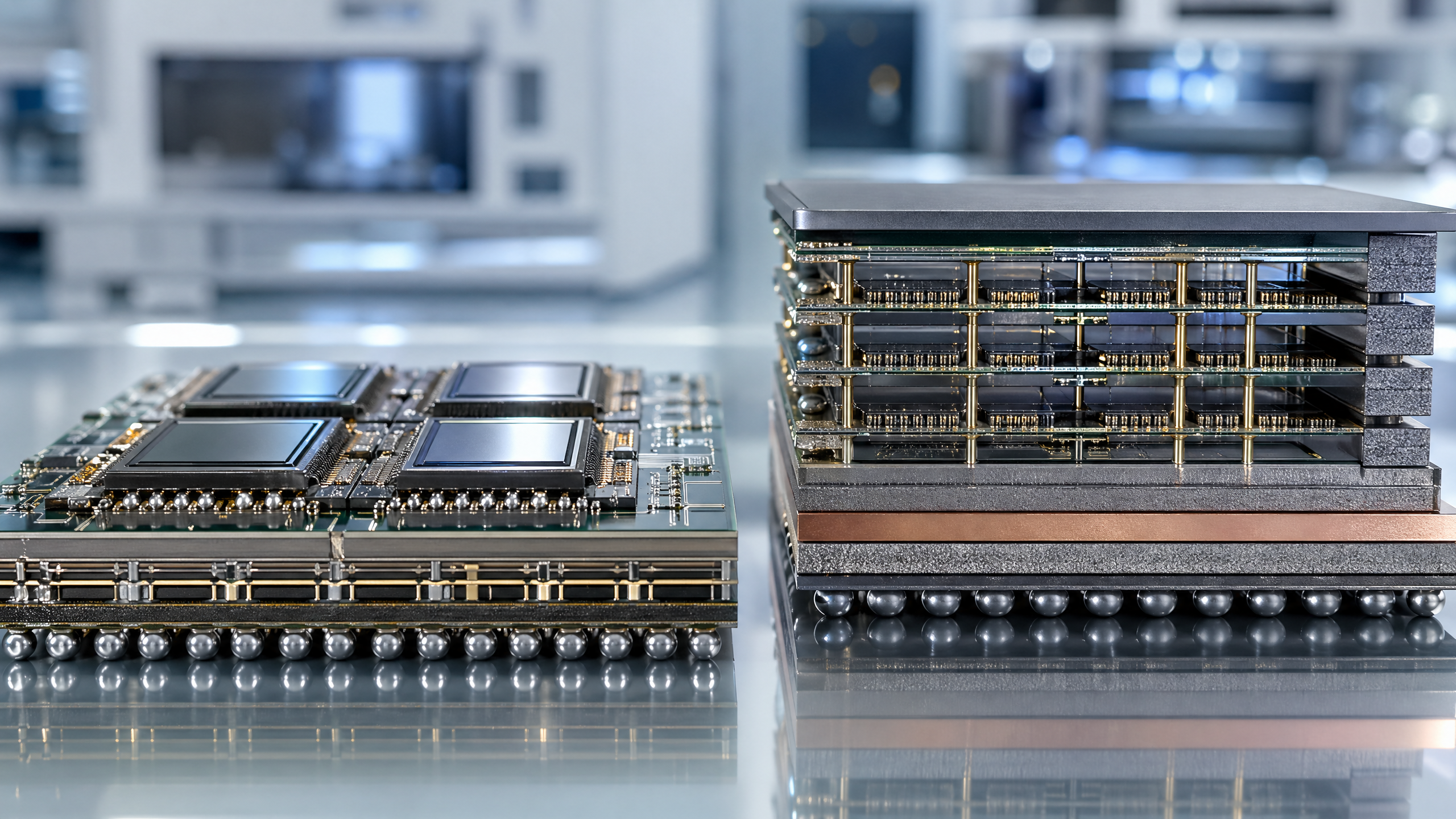
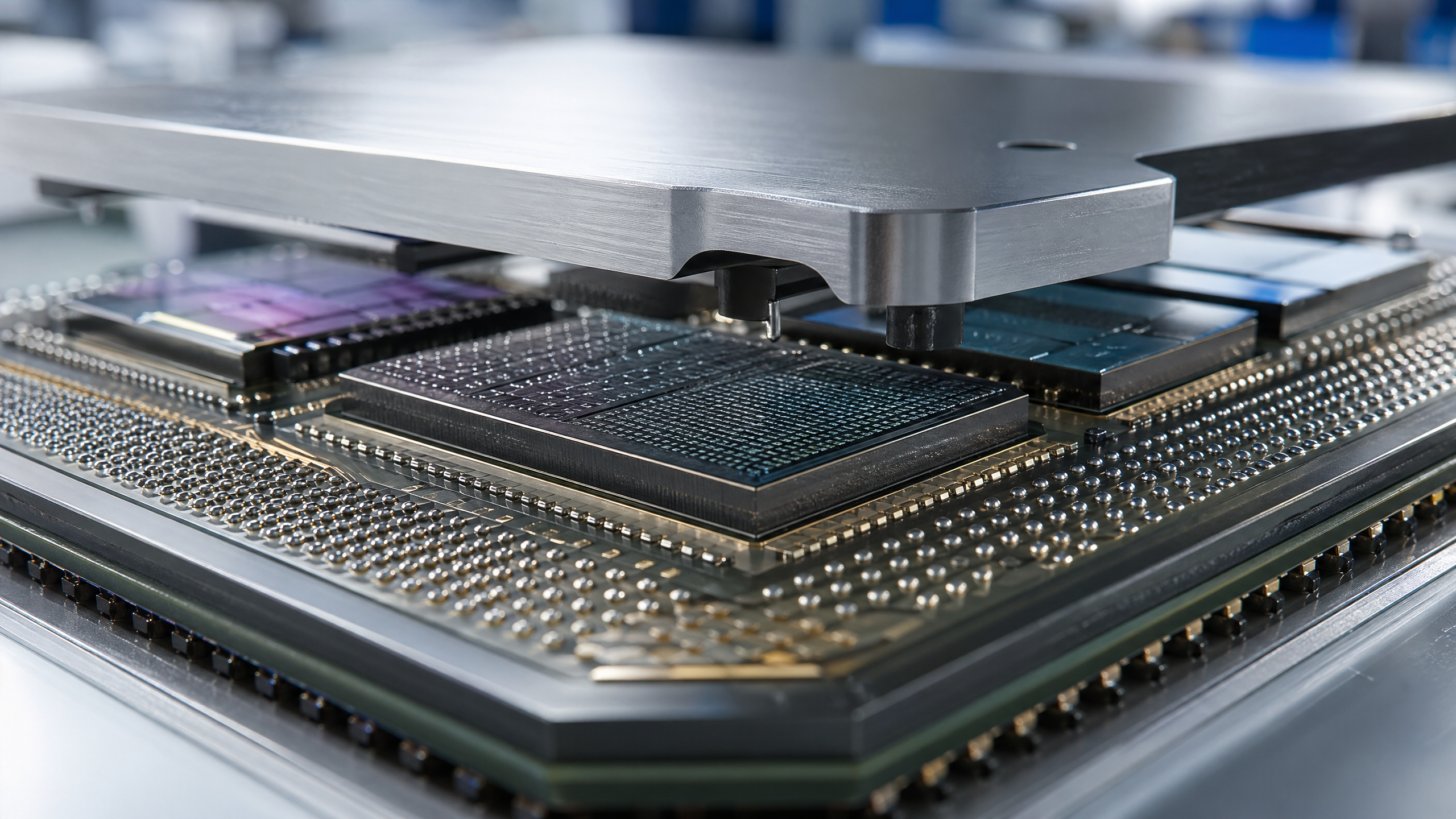
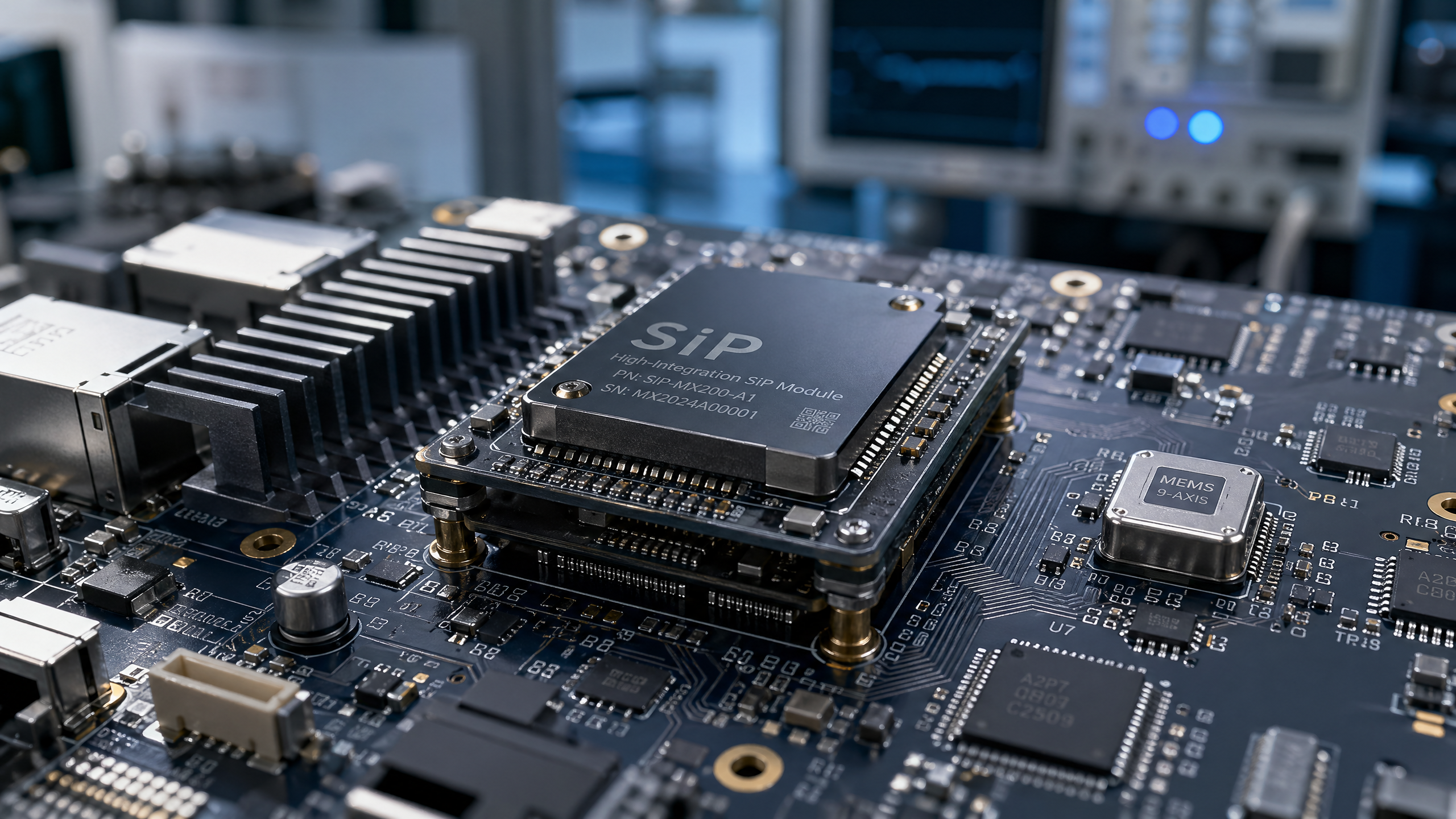
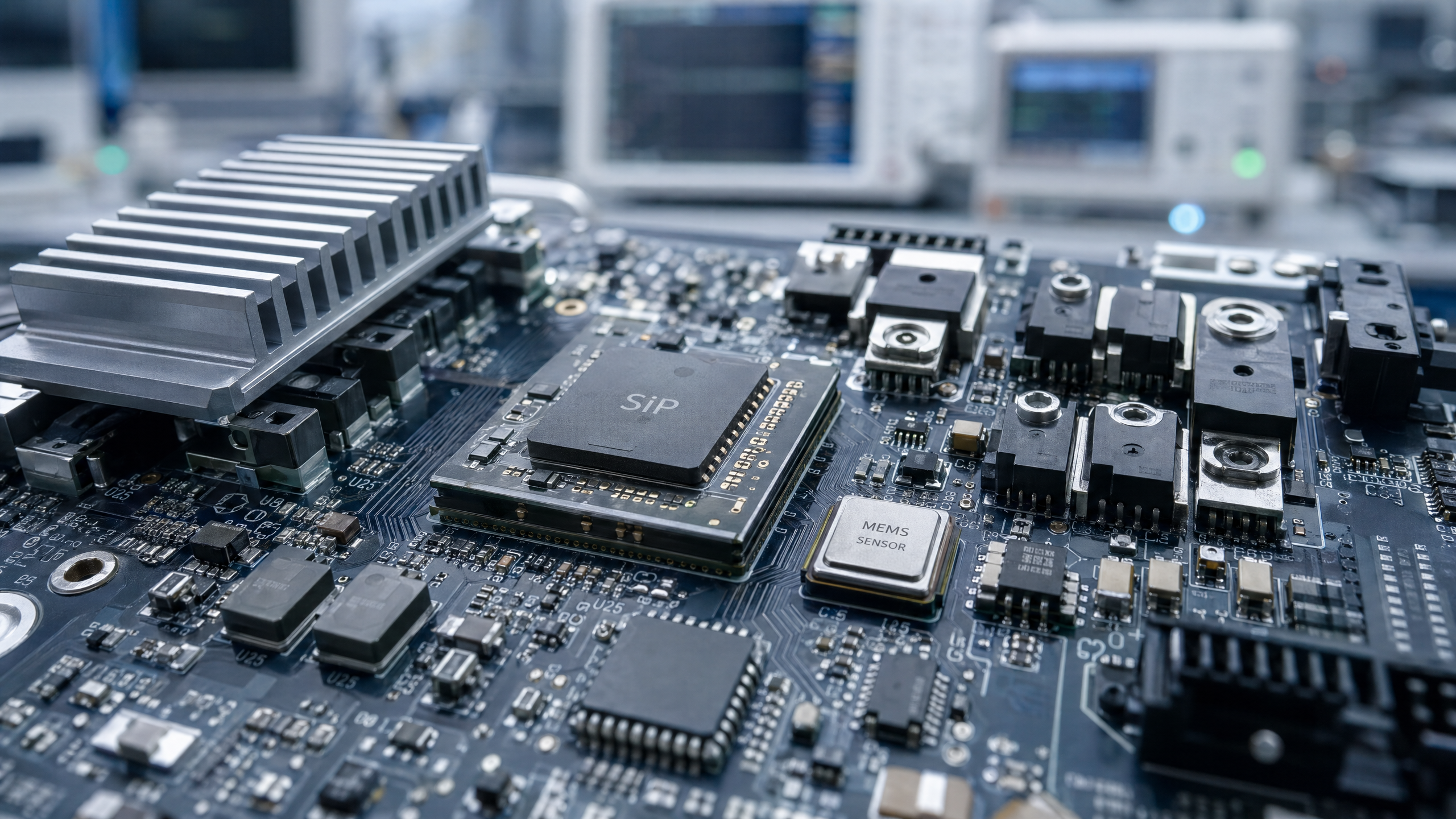
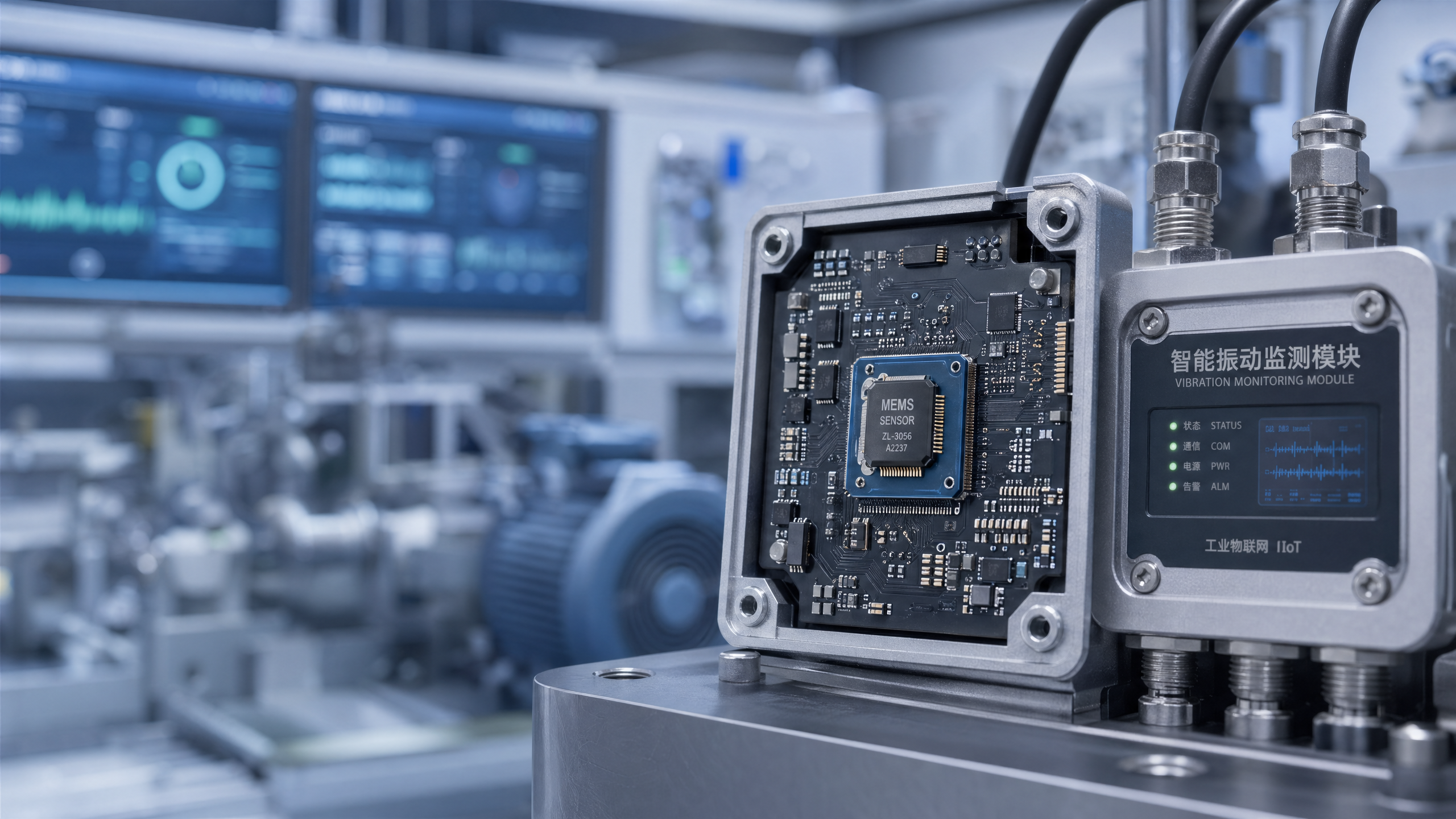
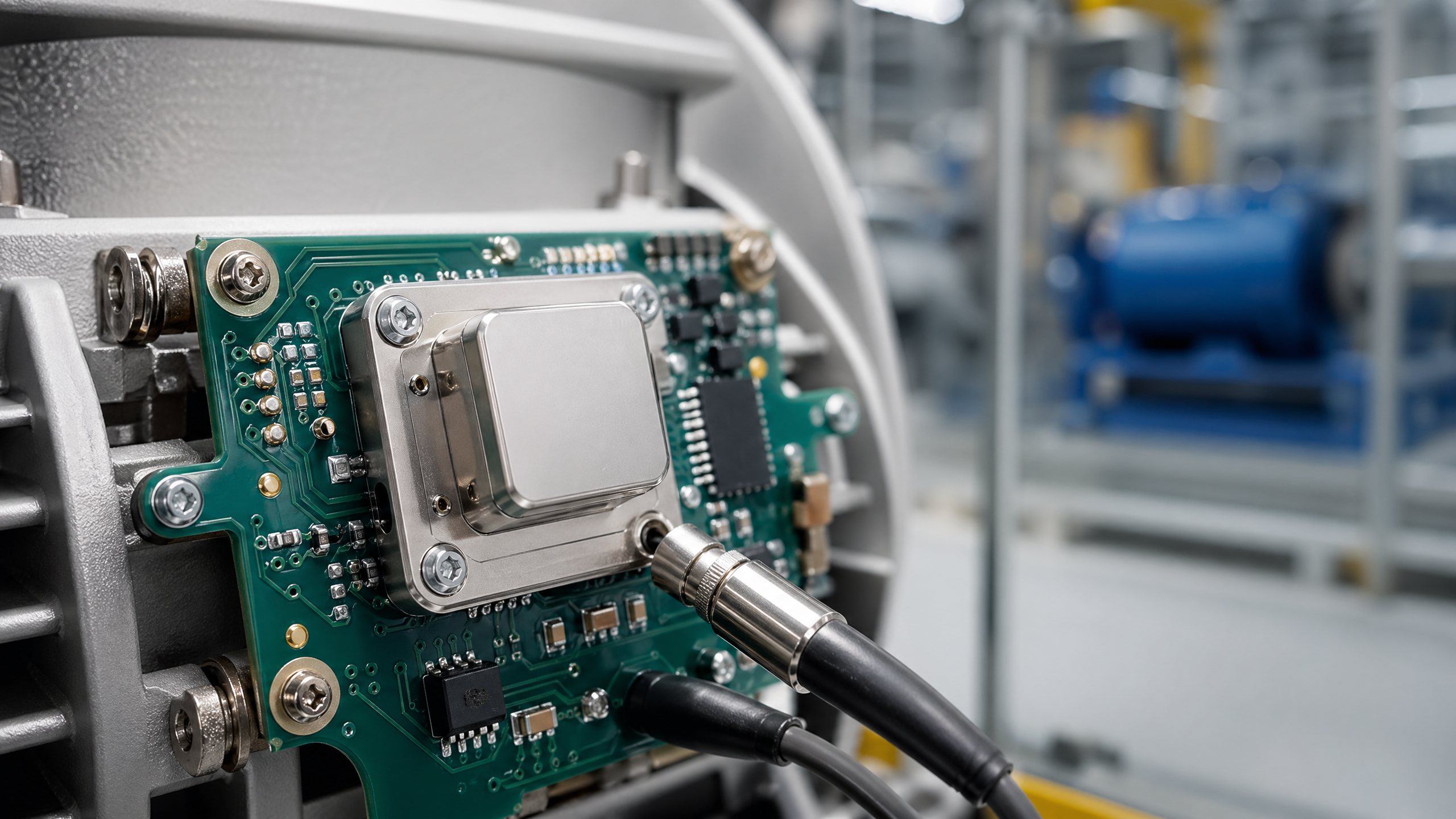
Industrial IoT security gaps often emerge where legacy devices intersect with Smart Sensors, MEMS Sensors, and expanding Digital Infrastructure. As Autonomous Systems scale across sectors, overlooked risks in Environment Control, IC Testing, and connected assets can weaken Supply Chain Resilience. For organizations deploying GaN and SiC MOSFET technologies, understanding these vulnerabilities is essential to building secure, reliable industrial operations.
For plant operators, technical evaluators, procurement teams, safety managers, and enterprise decision-makers, the problem is rarely a single cyber weakness. In most industrial environments, the real issue is the coexistence of 10-year-old controllers, unsupported field devices, modern edge gateways, and data-driven production systems that were never designed to trust each other securely.
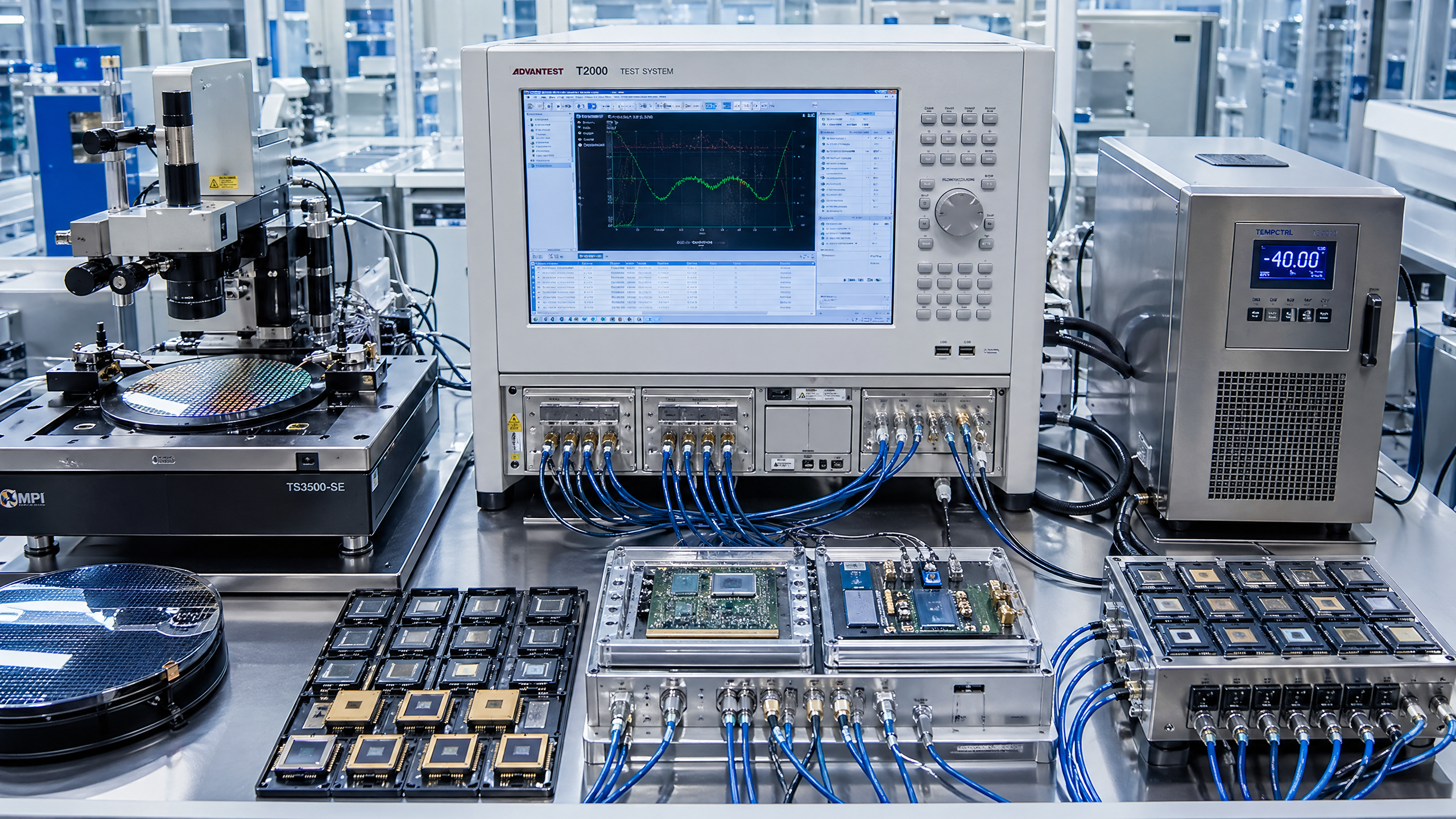
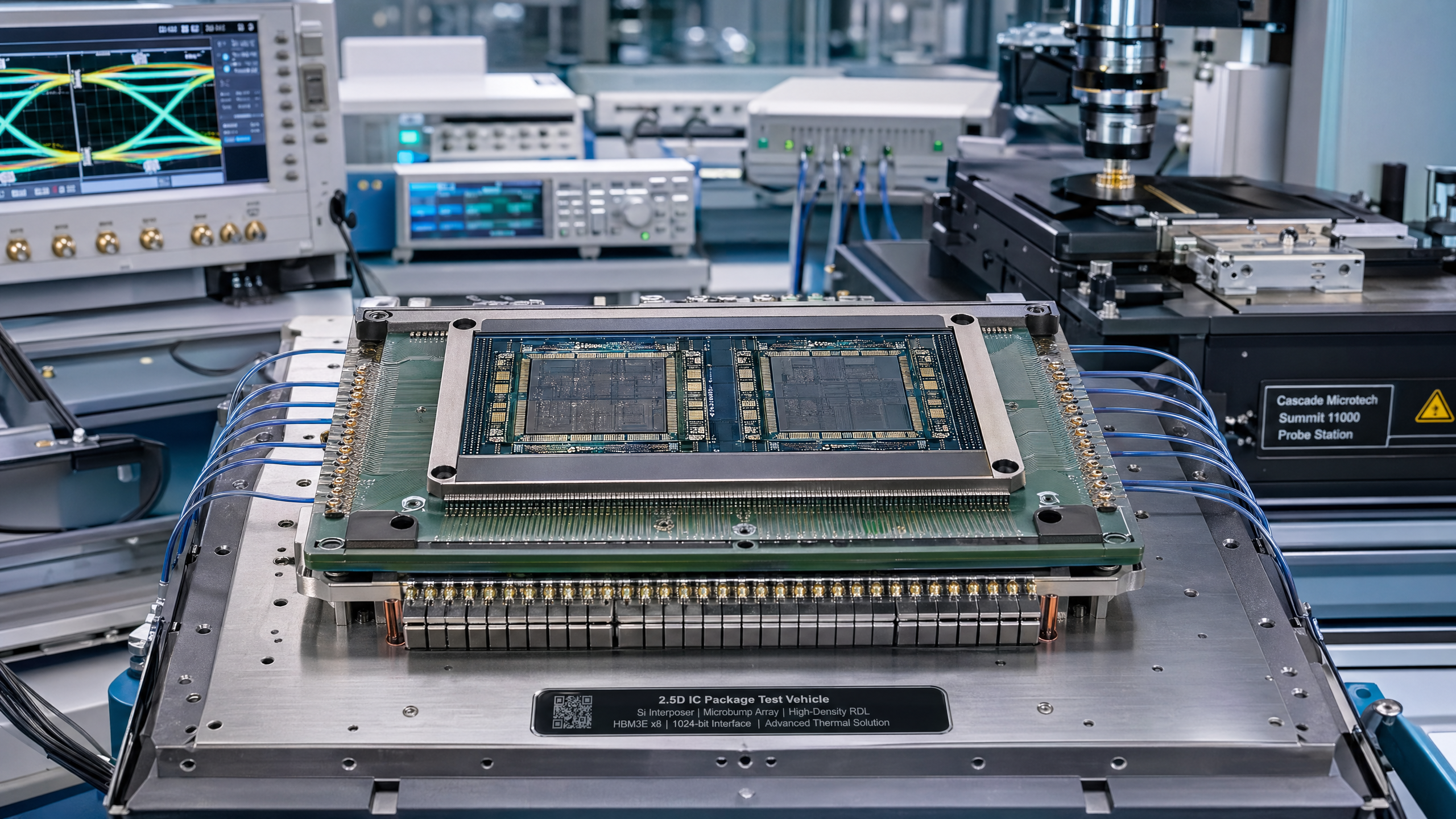
This challenge is especially relevant in semiconductor, sensing, and power electronics ecosystems, where uptime, thermal stability, process integrity, and signal accuracy directly affect yield and product reliability. From fabrication environment control to MEMS sensor networks and IC testing lines, legacy assets often become the silent entry point for Industrial IoT security gaps.
For stakeholders using G-SSI as a strategic reference, the priority is not simply replacing old equipment. It is identifying where risk concentrates, defining practical mitigation paths, and aligning connected infrastructure with operational, quality, and supply chain requirements.
Why legacy devices remain the weakest link in Industrial IoT security
Legacy devices are still common across manufacturing, utilities, logistics, energy conversion, electronics assembly, and semiconductor support systems. Many are reliable from a mechanical or process-control perspective, yet they lack secure boot, encrypted communication, signed firmware, or role-based access control. A controller installed 8–15 years ago may still regulate critical equipment well, but it was not built for today’s connected industrial environment.
In Industrial IoT deployments, these older assets are frequently connected through protocol converters, remote maintenance tools, unmanaged switches, or edge collectors. Each integration layer adds value, but also increases the attack surface. A single unpatched HMI, a default password on a PLC, or a serial-to-Ethernet bridge without segmentation can expose production data, maintenance workflows, and even safety-relevant systems.
The issue is not limited to direct cyber compromise. Legacy devices can create indirect security gaps by generating incomplete logs, weak timestamps, or inconsistent telemetry. In sectors that depend on precise sensor data, a 2–3 second delay, an unstable calibration cycle, or a missing event record can slow incident response and reduce trust in operational decisions.
For G-SSI-aligned organizations operating in semiconductor and sensory infrastructure, this matters because process quality and digital trust are deeply linked. If environmental monitoring, gas handling interfaces, IC testing stations, or packaging lines depend on outdated endpoints, security risk can quickly become a quality risk and then a commercial risk.
Common sources of hidden exposure
The following patterns appear repeatedly across multi-vendor industrial sites, especially where modernization has happened in phases over 3–7 years rather than as a full redesign:
- Devices still using unsupported operating systems or firmware with no security patch path.
- Field equipment that communicates over Modbus, CAN, or serial interfaces without authentication.
- Engineering workstations shared by multiple technicians across 2 or more production zones.
- Remote support connections enabled permanently instead of through time-limited approval windows.
- Environmental and sensor networks added for analytics without full network segmentation.
These conditions do not automatically mean an incident will occur, but they do lower the effort required for unauthorized access, lateral movement, or process disruption.
How security gaps affect sensors, environment control, and power electronics operations
Industrial IoT security is often discussed at the enterprise network level, yet the operational impact usually appears closer to the process edge. In MEMS sensor networks, smart sensing nodes, and environmental monitoring systems, data integrity is as important as system availability. If readings are altered, delayed, or lost, operators may respond to false conditions or miss real anomalies.
In semiconductor-adjacent environments, stable control of temperature, humidity, particle levels, airflow, and gas purity is essential. Many facilities monitor these parameters in intervals ranging from 1 second to 60 seconds depending on process sensitivity. A legacy gateway or controller with weak security can become the path through which attackers, malware, or unauthorized users interfere with monitoring or setpoint coordination.
The same applies to IC testing and advanced packaging lines. Test handlers, burn-in systems, thermal chambers, and inspection stations often combine new analytics software with older machine control architecture. If those layers are not segmented, a compromise in one workstation can affect scheduling, traceability, calibration history, or test result credibility.
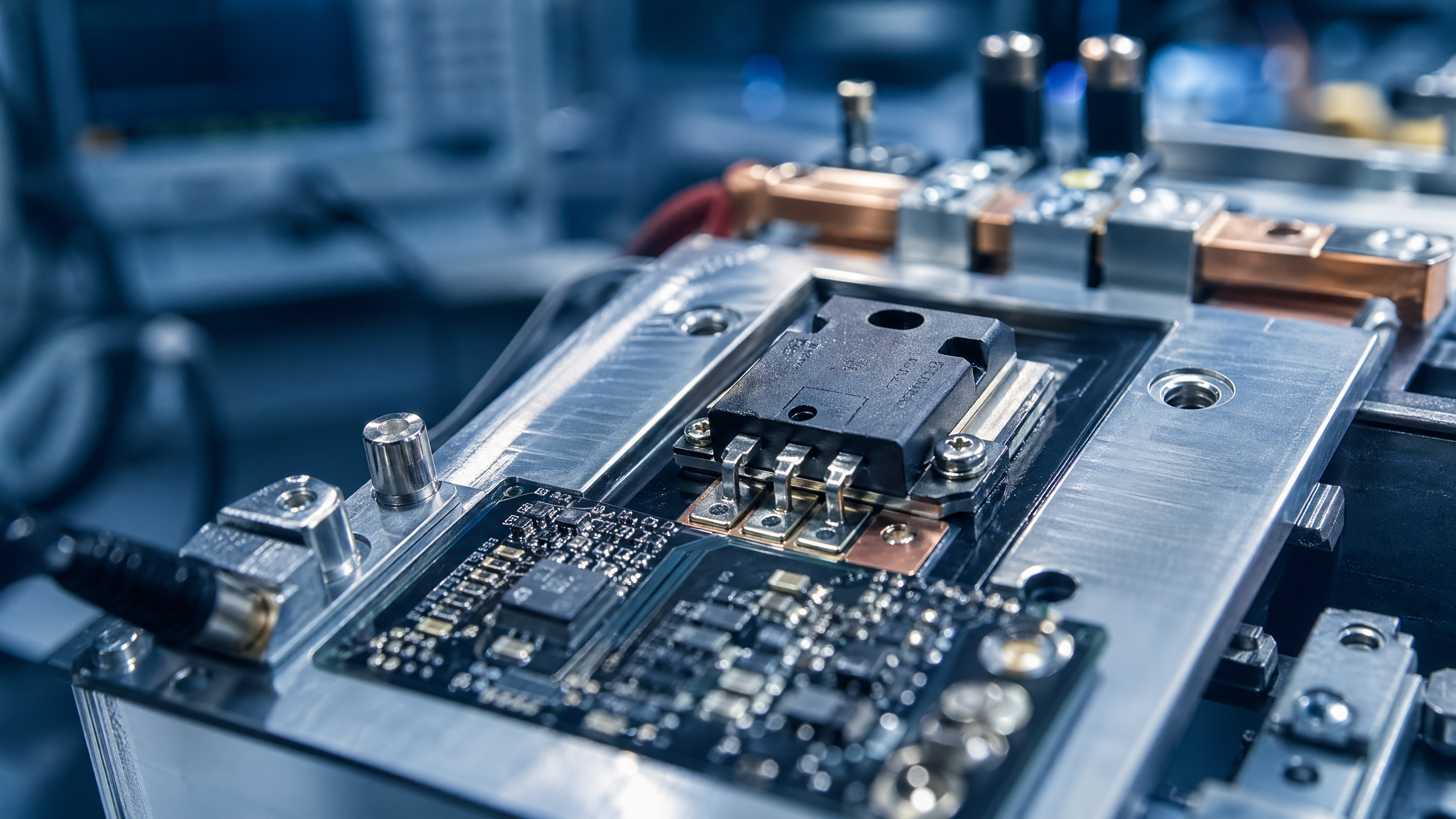
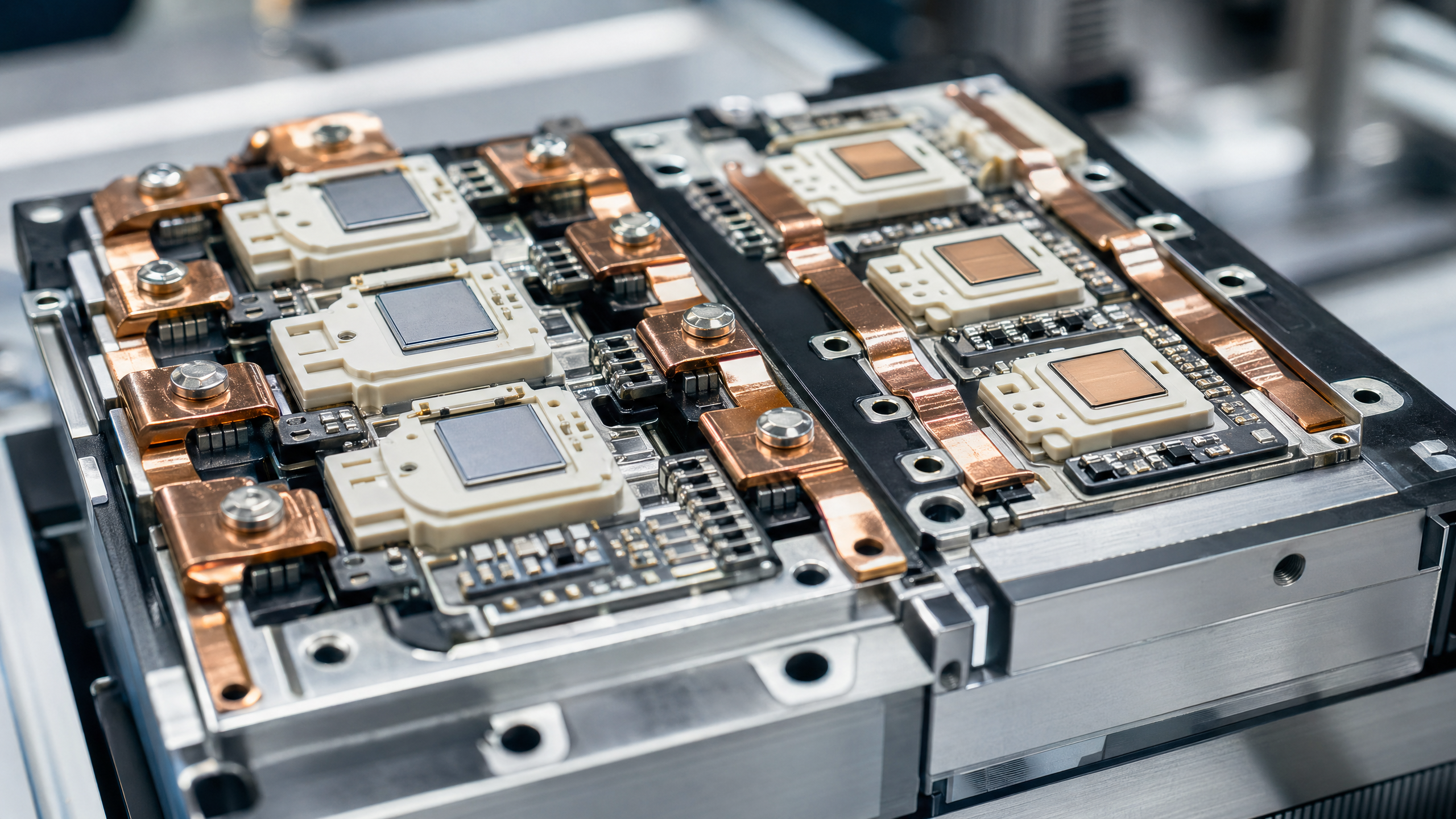
For organizations adopting SiC MOSFET and GaN power technologies, the risk profile can be even more demanding. These applications often involve high-voltage switching, fast transient behavior, thermal management sensitivity, and strict validation workflows. A security event that interrupts data collection or modifies process variables can delay qualification cycles by days or weeks.
Operational impact by asset type
The table below shows how different legacy-connected industrial assets can create different types of security and business exposure.
The key takeaway is that security gaps in legacy devices do not stay isolated. They propagate into uptime, calibration confidence, lot traceability, and customer delivery performance. That is why security review should be tied directly to operations, quality, and procurement decisions rather than treated as a separate IT exercise.
A practical framework for assessing legacy risk before modernization
A full rip-and-replace strategy is rarely realistic. In many industrial settings, replacement cycles range from 5–12 years for controls and 7–20 years for specialized process assets. The better approach is to rank legacy devices by operational criticality, cyber exposure, and recoverability. This gives project managers and procurement teams a path to prioritize investment without interrupting production unnecessarily.
An effective assessment typically begins with asset discovery. Many organizations know their main production equipment but lack a verified inventory of gateways, engineering laptops, unmanaged switches, firmware versions, and temporary remote access tools. Without that baseline, it is difficult to know which connections support the business and which simply remain from past upgrades.
The second step is mapping trust boundaries. Teams should identify where production networks, lab systems, vendor access paths, and enterprise systems intersect. In practice, 4 zones are usually enough for an initial model: critical process control, operational monitoring, engineering and maintenance, and business IT integration. Even this basic structure often reveals high-risk pathways that were previously invisible.
The third step is defining mitigation options by device category. Some devices can be patched, some can be segmented, some need protocol mediation, and some require planned retirement within 12–24 months. The point is to avoid treating every legacy endpoint the same way.
Four-step evaluation model
- Build a verified asset list including device role, firmware age, network exposure, and maintenance owner.
- Score each asset on three dimensions: process criticality, exploitability, and recovery effort.
- Assign one of four actions: monitor, segment, harden, or replace.
- Review results every 6–12 months or after major line changes, supplier changes, or remote access updates.
Assessment criteria for procurement and engineering teams
The following matrix can help cross-functional teams evaluate legacy-connected devices in a way that supports budgeting, security planning, and quality assurance.
This model helps decision-makers avoid one common mistake: spending on isolated devices while leaving higher-risk connectivity pathways untouched. In most environments, segmentation and access control deliver faster risk reduction in the first 90 days than random hardware replacement.
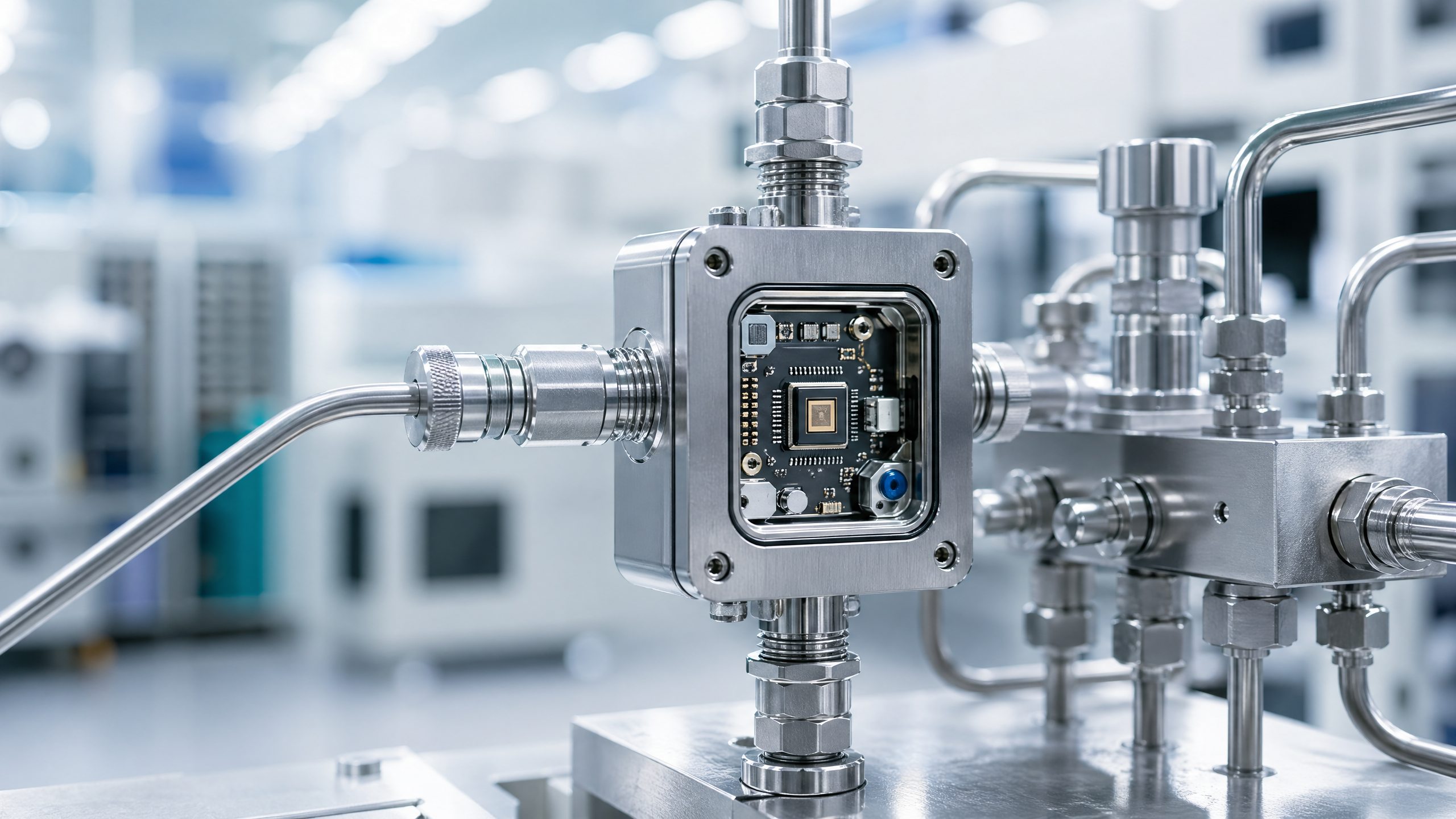
What secure modernization looks like in semiconductor and sensory infrastructure
Secure modernization is not a single product purchase. It is a staged program that protects current operations while improving long-term resilience. In semiconductor and sensory infrastructure, that usually means balancing 3 goals at the same time: maintaining uptime, preserving data fidelity, and enabling future automation.
For many organizations, the first stage is containment. This includes network segmentation, device inventory validation, password governance, time-limited remote access, and secure jump-host design. These actions can often be implemented within 4–8 weeks and may reduce immediate exposure without touching validated process logic.
The second stage is controlled hardening. That may involve gateway replacement, protocol wrapping, firmware review, backup standardization, and improved event logging for edge systems. In high-value environments such as packaging, clean utility monitoring, gas delivery support, and power module testing, better logging can shorten incident triage from several hours to less than 30 minutes.
The third stage is lifecycle redesign. This is where procurement, engineering, quality, and security teams align future purchases to a consistent baseline. New sensor platforms, environmental monitoring nodes, and process-connected controllers should be evaluated not only for function, but also for secure update support, auditability, role separation, and vendor maintenance commitments.
Baseline requirements for new deployments
- Support for unique user accounts and role-based access instead of shared operator credentials.
- Documented firmware support period, ideally with a maintenance window of at least 5 years.
- Secure logging with synchronized timestamps for alarms, configuration changes, and remote sessions.
- Separation between operational control traffic and analytics or enterprise reporting flows.
- Validation procedures for sensor calibration, data retention, and change management across 3 or more approval roles where required.
Role of standards and benchmarking
Organizations working with G-SSI priorities typically benchmark assets and processes against recognized industrial expectations such as SEMI practices, AEC-Q100 relevance in reliability-oriented workflows, and ISO/IEC 17025 principles where measurement integrity and calibration confidence matter. The goal is not to claim every asset must meet the same rule set, but to ensure that connected systems support the reliability, thermal control, and data quality expected in sovereign-grade digital infrastructure.
This is especially important when China-based mature-node expansion, global sourcing, and cross-border technical collaboration come together in one supply chain. A device that is operationally acceptable in isolation may still be a weak point when integrated into a broader, internationally benchmarked infrastructure.
Procurement, project delivery, and common mistakes to avoid
Industrial IoT security gaps often become procurement problems later than they should. Teams may buy sensors, edge platforms, or machine upgrades based on performance, cost, and delivery time, but fail to specify recovery requirements, remote access rules, or support obligations. When that happens, a project can meet functional targets and still introduce hidden risk for the next 5 years.
For buyers and project owners, one of the most practical questions is this: what happens if the device fails, is compromised, or needs urgent reconfiguration during production? If the answer depends on one engineer, one laptop, or one vendor-only tool, the operational risk is already too concentrated.
Lead times also matter. A secure modernization plan should account for 2–6 weeks for site assessment, 4–12 weeks for network and gateway changes, and longer for equipment retirement if validation is required. In regulated or quality-sensitive production, the approval cycle may take as long as the technical implementation itself.
Distributors, agents, and solution partners can add value when they help end users compare lifecycle support, spare strategy, and integration effort rather than only unit price. In many cases, the lower-cost device becomes more expensive after 18–24 months if it lacks secure maintenance support or creates repeated engineering overhead.
Common selection mistakes
- Choosing IIoT gateways without checking whether they support logging, certificate management, and segmented deployment.
- Allowing permanent remote access because it is convenient during commissioning.
- Assuming sensor accuracy and cybersecurity are separate topics, even when both affect data trust.
- Retaining legacy engineering workstations on shared networks after new systems are added.
- Replacing devices one by one without redesigning the network zones around them.
FAQ for buyers, engineers, and operators
These are some of the most common practical questions raised during Industrial IoT security planning.
How do we know whether a legacy device should be replaced or segmented?
If the asset is highly critical, internet-exposed, unsupported, and difficult to recover within 8 hours, replacement planning should begin immediately. If it remains operationally stable but lacks modern security features, segmentation and access control may be the faster short-term option.
Which environments face the highest risk from inaccurate sensor data?
High-risk environments include clean utilities, thermal process control, gas monitoring, predictive maintenance systems, and IC testing flows where timing, calibration history, and traceability affect qualification or shipment decisions.
How often should asset and access reviews be performed?
As a practical baseline, review critical connected assets every 6 months and remote access paths every 90 days. Additional review should occur after vendor changes, firmware updates, line expansion, or network reconfiguration.
What should be included in a supplier evaluation?
Ask about patch policy, firmware support period, backup and restore procedures, logging capability, credential management, remote support method, spare part availability, and expected support response time. These details often matter more than small differences in upfront pricing.
Legacy devices will continue to exist across Industrial IoT environments because they still perform useful work, but their security assumptions no longer match the realities of connected operations. The real task is to identify where those assumptions create risk for process continuity, sensor integrity, and supply chain resilience.
For organizations operating across semiconductor fabrication support, advanced packaging, smart sensing, power electronics, and industrial environment control, a disciplined assessment and phased modernization strategy can reduce risk without unnecessary disruption. G-SSI’s benchmarking perspective is valuable here because it connects device-level security decisions to larger goals such as reliability, thermal performance, data fidelity, and sovereign-grade infrastructure readiness.
If your team is evaluating legacy-connected assets, planning secure sensor deployment, or aligning procurement with future Industrial IoT requirements, now is the right time to define a practical roadmap. Contact us to discuss your environment, request a tailored assessment framework, or explore solutions that improve both operational security and technical resilience.
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.